Secure Access Service Edge is the future of SD-WAN
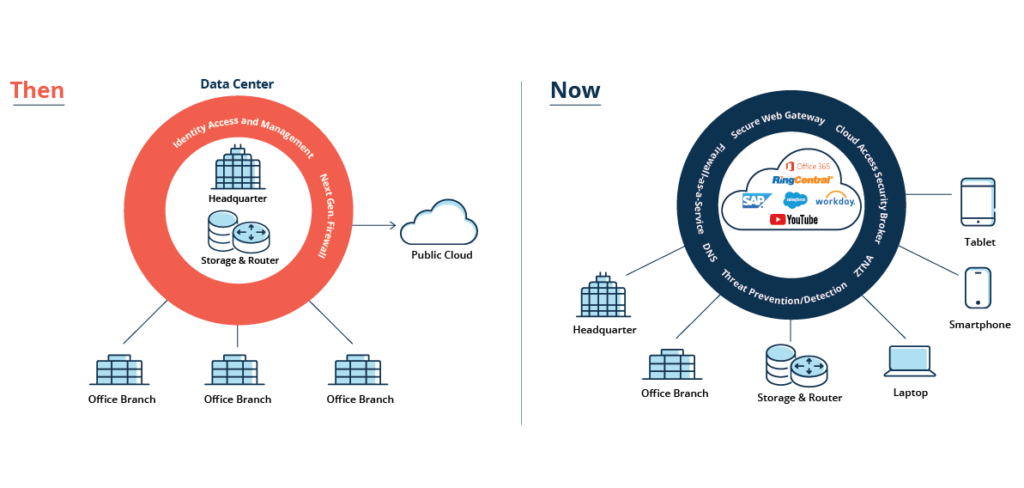
Secure access service edge (SASE) is a framework for network architecture that brings cloud native security technologies—SWG, CASB, ZTNA, and FWaaS in particular—together with wide area network (WAN) capabilities to securely connect users, systems, and endpoints to applications and services anywhere. To support today’s agile operations, these are delivered as a service from the cloud and can be managed centrally.
Digital business transformation demands greater agility and scalability coupled with reduced complexity and improved security. What’s more, modern enterprises need to ensure their users are getting the best experiences from anywhere.
Components of a SASE Model
SASE can be broken down into 9 essential elements in terms of its capabilities and technologies.
- Software-Defined Wide Area Network (SD-WAN) :
SD-WAN is an overlay architecture that reduces complexity and optimizes the user experience by selecting the best route for traffic to the internet, cloud apps, and the data center. It also enables rapid deployment of new apps and services and helps you manage policies across a large number of locations. - Secure Web Gateway (SWG):
SWGs prevent unsecured internet traffic from entering your internal network. It shields your employees and users from accessing and being infected by malicious web traffic, vulnerable websites, internet-borne viruses, malware, and other cyber threats. - Cloud Access Security Broker (CASB):
CASBs prevent data leaks, malware infection, regulatory noncompliance, and lack of visibility by ensuring safe use of cloud apps and services. They secure cloud apps hosted in public clouds (IaaS), private clouds, or delivered as software-as-a-service (SaaS). - DLP: Data loss prevention limited to Network:
Network Data Loss Prevention solutions to prevent leakage of sensitive information via the network. An effective Network Data Loss Prevention (DLP) solution monitors, detects and potentially blocks sensitive data exfiltration while the data is in motion across the network using various protocols or when it is residing on popular cloud repositories.
Network DLP is also used to enforce regulations required by certain industries to ensure that Enterprise organizations are able to demonstrate adequate care to avert the loss or theft of confidential and sensitive information. Examples of such regulations can be to provide protection of personal health records in health industry (via HIPAA), financial records in financial industries (PCI, SOX) and many more. Hence it is expected for Network DLP solutions to support different data formats and types to support such well-defined, industry specific data formats and types to comply with the requirements of each of these market verticals. - Firewall as a Service (FWaaS):
FWaaS helps you replace physical firewall appliances with cloud firewalls that deliver advanced Layer 7/next-generation firewall (NGFW) capabilities, including access controls, such as URL filtering, advanced threat prevention, intrusion prevention systems (IPS), and DNS security. - Zero Trust Network Access (ZTNA):
ZTNA products and services give remote users secure access to internal apps. With a zero trust model, trust is never assumed, and least privileged access granted based on granular policies. It gives remote users secure connectivity without placing them on your network or exposing your apps to the internet. - Cloud Browser Isolation:
Remote browser isolation (RBI) is a web security technology that neutralizes online threats by hosting users’ web browsing sessions on a remote server instead of the user’s endpoint device. RBI separates web content from the user’s device to reduce its attack surface. - Cloud Sandbox:
cloud sandboxing eliminates the need for localized servers and enables URLs, downloads, or code to be easily tested on-demand in a virtual sandbox, completely separated from the computer or any of the network devices. - Centralized Management:
Managing all of the above from a single console lets you eliminate many of the challenges of change control, patch management, coordinating outage windows, and policy management while delivering consistent policies across your organization, wherever users connect from.